AML programs have grown vast and expensive, yet criminals still move money with alarming success. Global financial institutions spend well into the hundreds of billions each year on financial crime compliance, but recovery rates for illicit funds remain negligible and false positives swamp operations. The gap between effort and impact signals a simple truth for senior banking leaders: the current AML playbook has reached end of life. It is time to rebuild for outcomes, not activity.
NextGen AML is a shift in operating model, not a new piece of software. It is enabled by modern data and technology, and governed with discipline. The goal is a clear and measurable disruption of criminal value chains, not more alerts, forms, or headcount.
Why the Current Playbook Fails
Most AML dashboards track alerts closed, SARs filed, and customers screened. These are inputs. They say little about criminal disruption, asset recovery, time-to-freeze, or repeat-offender suppression.
One size fits none. Factory-style controls treat a micro-merchant and a multinational similarly. The result is friction for low-risk customers and blind spots where sophisticated networks actually operate.
Fragmented intelligence. Banks hold only a slice of the picture. Other slices sit with peer institutions, regulators, and law enforcement. Siloed insights mean criminals exploit seams between organizations.
Legacy tech under strain. Batch-based monitoring, brittle rules, and static Know Your Customer processes cannot keep pace with fast-moving typologies. According to PricewaterhouseCoopers, 90-95% of all risk alerts through AML monitoring tools are false positives. This forces teams to triage noise rather than surface real risk.
Rising cost, stagnant outcomes. Global financial institutions invest approximately $206 billion annually to comply with financial crime compliance standards, with little change in seizure rates relative to total illicit flows.
The Five Drivers of NextGen AML
Ecosystem-Driven Operating Model
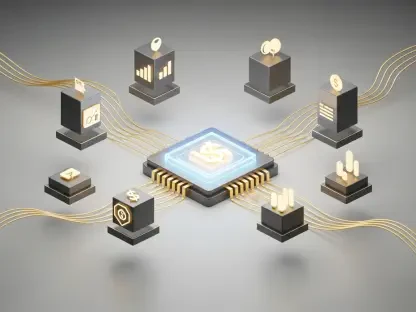
Financial crime is an ecosystem problem, so the operating model must reflect that reality. This starts with shared threat priorities, common definitions, and structured channels for information exchange among banks, non-bank financial institutions, regulators, and law enforcement.
Align on priority threats. Map national or regional priorities to institutional risk appetites and control design. Focus resources where they can materially disrupt trafficking, corruption, and fraud supply chains, not only where it is administratively convenient. The U.S. Treasury’s 2024 National Money Laundering Risk Assessment identifies the top money laundering threats as fraud, drug trafficking, cybercrime, corruption, human trafficking, human smuggling, and professional money laundering, providing institutions with explicit national priorities to which they can align risk assessments and control frameworks.
Build trusted utilities. KYC and screening utilities, industry typology exchanges, and negative-news services reduce duplication and improve consistency. Utilities should offer robust governance, data minimization, and clear participation rules.
Formalize collaboration. Public-private partnerships must move beyond ad hoc roundtables to defined workstreams with service levels. That includes data request templates, feedback on SAR utility, and joint exercises to test typology coverage.
Respect boundaries. Ecosystem collaboration cannot outrun the law. Ensure legal bases, consent mechanisms, and privacy-by-design are embedded from the start, especially for cross-border data use.
Intelligence-Driven Orchestration
Move from blanket controls to precision risk targeting. Think spearfishing, not trawling.
Threat-informed design. Start with current typologies, cross-sector incidents, and law-enforcement feedback. Translate these into monitoring hypotheses and case narratives. Continuously refresh them as adversaries adapt.
Dynamic segmentation. Segment customers by behavior, geography, product use, and network affiliations. Use that segmentation to route monitoring, outreach, and periodic reviews. Low-risk segments receive light-touch oversight, while high-risk segments receive deeper scrutiny with richer data.
Priority queues and escalation. Orchestrate investigative work based on potential harm, not arrival time. Alerts that align with priority threats should jump the line with enhanced data context.
Human-in-the-loop, by design. Analysts validate and refine models, contribute new patterns, and help calibrate thresholds. The loop turns analyst judgment into institutional intelligence, not anecdote.
Output-Driven Supervision and KPIs
If leadership rewards volume, they will get volume. If leadership rewards disruption, behavior will change.
Replace vanity metrics. De-emphasize alerts closed, rules deployed, and time-to-file for filings that yield no action.
Track impact. Prioritize measures such as conversion from alert to law enforcement action, asset recovery per operational dollar, time-to-freeze for high-risk networks, and reduction in repeated suspicious activity for the same entities.
Close the feedback loop. Require structured feedback from law enforcement on SAR utility and case outcomes. Where possible, negotiate anonymized feedback summaries that allow model tuning without exposing case-sensitive details.
Align with regulators. Encourage supervisory focus on outcomes and explain how the program measures and manages toward those outcomes. Regulators like the Hong Kong Monetary Authority have issued guidance encouraging banks to utilize AI for enhancing the monitoring of money laundering and terrorist financing risks, highlighting that AI-based systems can have clear advantages over traditional rules-based approaches in detecting complex, atypical patterns of suspicious activity, signaling openness to innovation where firms can demonstrate robust governance and risk control.
Data-Driven Foundation
AML is a data discipline. The foundation determines the ceiling.
Entity resolution as a first principle. Build persistent, privacy-safe entity and relationship graphs that reconcile customers, counterparties, and beneficial owners across systems. Accurate entity resolution reduces noise, supports network analytics, and sharpens screening.
Standardize taxonomies. Harmonize reason codes, disposition categories, and typology tags. Consistent labels enable learning across teams and time.
Quality with teeth. Establish data quality SLAs for critical fields, profile lineage, and automate controls to prevent degradation. Incentivize data producers to fix root causes, not only remediation teams to clean up symptoms.
Privacy-preserving analytics. Use techniques such as federated learning, secure enclaves, and differential privacy for cross-institution typology discovery where permitted. These approaches can improve detection without raw data pooling.
Beneficial ownership facts. New disclosure regimes have expanded access to ownership data, but the accuracy and update frequency vary. Integrate these registries thoughtfully, with corroboration and aging logic. In the United States, the Corporate Transparency Act’s Beneficial Ownership Information E-Filing System became operational on January 1, 2024, requiring certain businesses to file beneficial ownership information with FinCEN to enhance corporate transparency and prevent the misuse of legal entities, which affects Know Your Customer refresh strategies. However, institutions should note that U.S. domestic company requirements were subsequently suspended in March 2025.
Technology Strategy with Guardrails
Technology can accelerate progress, but only if it is purposeful and governed.
Modern analytics stack. Combine graph analytics, anomaly detection, and supervised models. Use rules where they excel, such as codifying non-negotiable red flags, and use models where patterns are complex or contextual.
Explainability and reviewability. Select techniques that produce features and rationales that analysts and model risk teams can evaluate. Embed challenge processes and champion-challenger testing.
Responsible AI. Treat AI components as governed services with SLAs, not as opaque helpers. Define performance, latency, stability, and fairness requirements. Document data provenance and model lineage.
Case automation and copilot tools. Use LLMs to summarize long narratives, extract entities from documents, and draft consistent case notes. Keep humans accountable for decisions, especially where customer outcomes are affected.
Cloud and interoperability. Design for portability to avoid vendor lock-in. Use open data interfaces so typology updates and feedback can flow across tools and teams.
Practical Trade-Offs and Cost Realities
Modernizing entity resolution, data quality, and case management requires a significant upfront investment, with expected savings only materializing over time due to reduced manual effort. Additionally, managing model governance involves crucial activities like explainability and testing. Organizations need to enhance model risk management and internal audit functions to avoid bottlenecks.
Data sharing is often restricted by privacy and localization regulations, necessitating federated approaches and strong access controls instead of broad data pooling. The vendor landscape is cluttered with point solutions; firms should ensure vendor contracts include open interfaces and measurable outcomes to avoid complex API connections.
Finally, the evolving regulatory landscape, including the new EU Anti-Money Laundering Authority from 2024, will increase supervision of high-risk financial institutions starting in 2028. Proactive engagement with these changes can help institutions shape expectations.
Markers of Progress for Senior Leaders
Outcomes become more apparent through the use of executive dashboards that display disruption metrics. These metrics include factors such as asset recovery per dollar and time-to-freeze, rather than just focusing on volume figures.
As workflows become more advanced, low-risk customers experience swifter processes while investigators can direct their efforts toward prioritizing significant threats. Furthermore, the triage process is grounded in evidence, allowing for more effective decision-making.
The feedback loop continuously improves as insights from law enforcement, analyst observations, and model telemetry converge into a singular enhancement cycle. This integration ensures that the system evolves based on real-world data and experiences.
As the intelligence behind these processes sharpens, organizations can simplify their controls. This allows them to phase out ineffective rules, reduce redundant checks, and focus their reviews on a select few critical areas that truly matter.
Conclusion
Financial crime exploits institutional seams, metric distortion, and compliance inertia. Incremental optimization of the existing AML playbook will not close those gaps. The operating model itself determines whether resources generate disruption or documentation.
NextGen AML is not a technology upgrade; it is a shift in what the institution optimizes for. Programs designed around audit defensibility produce activity volume. Programs designed around criminal disruption produce intelligence leverage. The two models differ in metrics, governance, talent profile, data architecture, and regulator engagement.
The strategic choice is unavoidable: continue scaling a control factory that measures effort, or redesign the system to measure harm reduction and asset denial. Both paths demand investment. A single change can alter the outcomes.